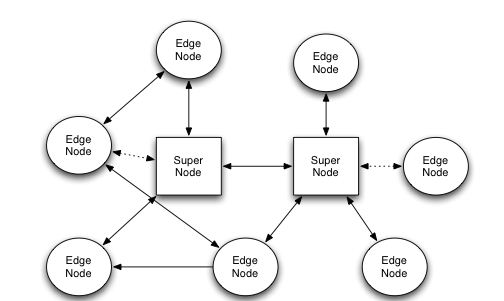
N2N is a layer 2 virtual private network that allows users to develop typical P2P applications on the network rather than at the application layer. This means that users can get local addresses transparently, and if the new IP address is on the same subnet, two machines can ping each other no matter where they are. N2N network architecture is divided into two parts: Super node and Edge node.
Super node: An application installed on devices with a common IP address that enables edge nodes to access other edge nodes behind a symmetric firewall.
Edge node: An application installed on a industrial wireless secure router or on a user's computer or phone that allows the construction of an N2N network. In effect, each edge node creates a Tun/Tap tunnel device that connects to the N2N network.
N2N Network Features
1. The N2N network acts as a layer 2 encryption network based on P2P
2. Encryption is done on the Edge node using the user's custom key. Users are in control of their security, not another public service provider.
3. Every N2N network user can belong to multiple networks at the same time.
4. Can be able to reverse traversal of NAT and firewall. Therefore, the edge node can be accessed even on the Intranet so that firewalls are no longer a barrier to direct communication at the IP level.
5. N2N networks are not designed to be independent networks and can route data between N2N network and non-N2N networks.
Four-Faith has launched the premium version of the industrial wireless secure router F-R200. As an integrated product of intelligent IoT, F-R200 adopts multi-channel intelligent collection + high-speed processing + high-speed wireless transmission + full Netcom + dual-band WIFI coverage + local storage +DIN rail installation.
Double the number of access (or equipment), providing strong support for WIFI coverage and operation compatible with IEEE802.11b/ G/N/AC mode, effectively reducing network delay.